This post is the first part of a three-part series on proxy blocks, covering an introduction and history. (second part, third part)
Open proxies – shared IP addresses accessible anywhere through free or paid services – have been blocked on Wikimedia projects for over 18 years.
Since its inception the policy has remained unchanged, with growing costs to accessibility and equity that insofar has not seen widespread discussion.
“No open proxies”
In early 2004, the question of anonymizing proxies was discussed on the English Wikipedia’s mailing list, with few objections to prohibiting their usage.
Arguments in favor noted that proxies were often used by vandals to evade blocks placed on their previous IP addresses and accounts. (On Wikimedia projects, accounts and IP addresses (or ranges of IP addresses) can be blocked to prevent editing from them; this is the primary anti-abuse tool that administrators have.)
Arguments against the proposal discussed the necessity of users subject to censorship, specifically China’s “Great Firewall”, to use proxies to safely access the internet.
Consensus developed, among the dozen or so participants on the mailing list thread, to block editing from open proxies. This was enacted on the English Wikipedia, and in 2006 was created as a global policy, enshrined on Meta-Wiki’s “No open proxies” page.
In the 18 years since that first discussion, the dynamics of open proxies and the problems associated with blocking them have changed significantly.
What constitutes a proxy?
For the purpose of Wikimedia blocks, a proxy is generally anything that allows a user to connect to Wikimedia projects through an IP address other than that assigned to them by their Internet Service Provider (ISP). Instead of a usual residential or cellular IP address, which has some degree of consistency and is often based on location, Wikimedia servers see the IP address of the proxy service.
Today, various types of proxy connections, and connections often affected by proxy blocks, exist:
- Traditional Virtual Private Networks (VPNs)
- Routes traffic through the VPN’s server
- Private relays, such as iCloud Private Relay or in-browser VPNs (Edge, Opera)
- These have similar functionality to traditional VPNs, but are far more accessible and easier for customers to enable, especially when some services are leaning towards making this the default
- Peer to peer or residential proxies (p2p)
- Users route traffic through other users’ residential internet connections
- IP switching tools
- Changes the user’s IP address regularly
- Carrier-grade Network Address Translation (CGNAT)*
- Common in areas with older internet infrastructure, where many users share the same IPv4 address
- T-Mobile style IP assigning*
- When a user resets their connection, they are assigned an IP address on an entirely different IP range
*The latter two are not technically proxies, but are often caught up in proxy-type blocks.
T-Mobile IPs present a problem very similar to proxies, where any customer can switch their cellular connection off and back on again, and be assigned a new IP on a different range. This allows users to easily evade a block placed on a previous IP address. All T-Mobile ranges are blocked for this reason.
CGNAT IPs suffer from an opposite issue; instead of one person having access to hundreds of IP ranges, hundreds of people have access to only one IP address. Because there are so many people on very few IP addresses, if one person vandalizes or connects using a peer-to-peer proxy, this can result in the IPs being blocked, affecting everyone who was connecting through that IP.
These are reflected here:
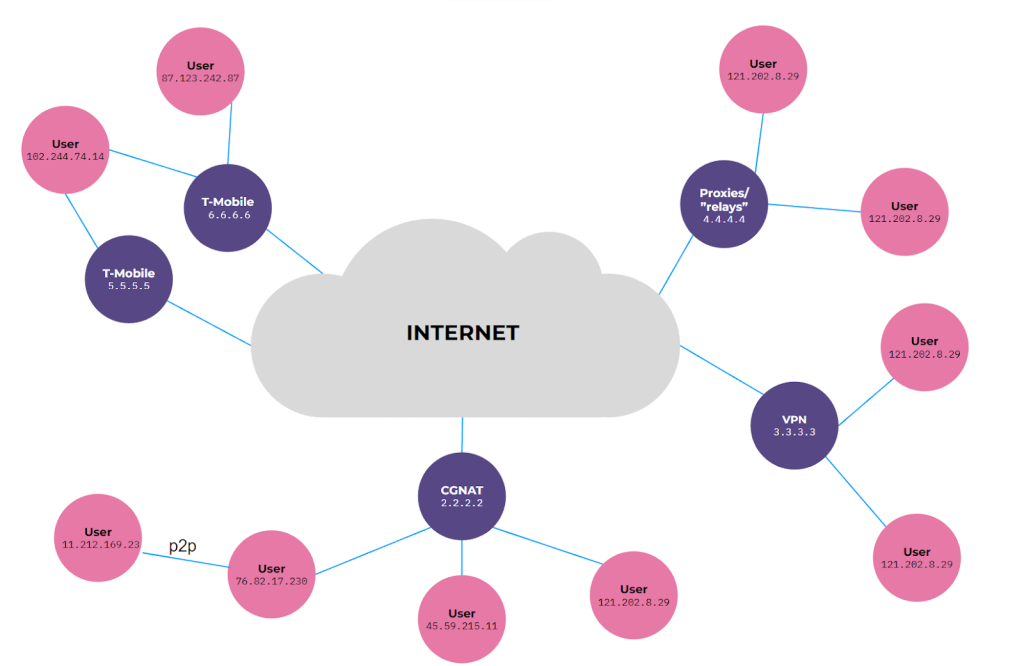
These types of connections vary in ease of identification, from traditional VPNs almost always being evident in IP lookups, to peer-to-peer proxies being difficult to distinguish from normal residential connections.
Why are proxies blocked?
The predominant reasons for blocking proxies have not changed since the initial discussion in 2004: their anonymizing effect prevents IP-based anti-abuse systems from working.
When someone connects to a proxy, they funnel their internet traffic through the servers of that proxy service. This means that Wikimedia servers see the IP address of that proxy service rather than the IP address assigned to them by their ISP.
Most proxy services provide dozens or hundreds of available connections, often in different countries (to evade geo-blocked content), to their customers. This is opposed to most residential ISPs, who assign singular IPs or relatively narrow ranges to their customers.
For example, my ISP assigns me a single IPv6 /64 subnet, which has been static for roughly 4 months. Searching it through Bullseye, a community-developed IP lookup tool, returns information about roughly my location, my ISP, and range. Were I to turn on a VPN, I could connect to servers in any region or country; and if one IP is blocked, I can switch to another. This makes static identification, and thus effective anti-abuse blocks, next to impossible for people using proxies.
Bad actors can use and rotate between open proxies to prevent identification of sockpuppets, evade IP address and range blocks, avoid scrutiny of contentious edits, or harass good faith editors. Where some websites may rely on cookies and other methods of tracking, MediaWiki anti-abuse tools nearly exclusively rely on IP addresses. Blocking open proxies is a necessity for functioning anti-abuse mechanisms on Wikimedia projects.
Though standard VPNs/proxies can be used to evade anti-abuse mechanisms, it is easy to identify when someone is using one, and to prevent editing from those IP ranges. Peer-to-peer proxies, however, evade this identification by funneling a user’s traffic through another user’s connection. This means that someone using a proxy in one country can appear to be connecting from a residential IP in another country. The next post in this series discusses the responses to the increasing prevalence of peer-to-peer proxies.

Can you help us translate this article?
In order for this article to reach as many people as possible we would like your help. Can you translate this article to get the message out?
Start translation